Did you know that Microsoft Agent 365 is generally available on May 1, 2026 and it is positioned as the control plane for AI agents across your enterprise?
If your organization is already running Copilot Studio agents, custom agents, or third-party agents, this launch is the moment to stop treating agents as individual projects and start managing them like a workforce.
 Agent 365 positions AI agents as a governable, securable workforce at enterprise scale.
Agent 365 positions AI agents as a governable, securable workforce at enterprise scale.
What Agent 365 is (and is not)
Agent 365 is not another agent builder. It is the governance, security, and observability layer that sits over every agent in your environment, regardless of where it was built.
At GA, the value is centered on five pillars:
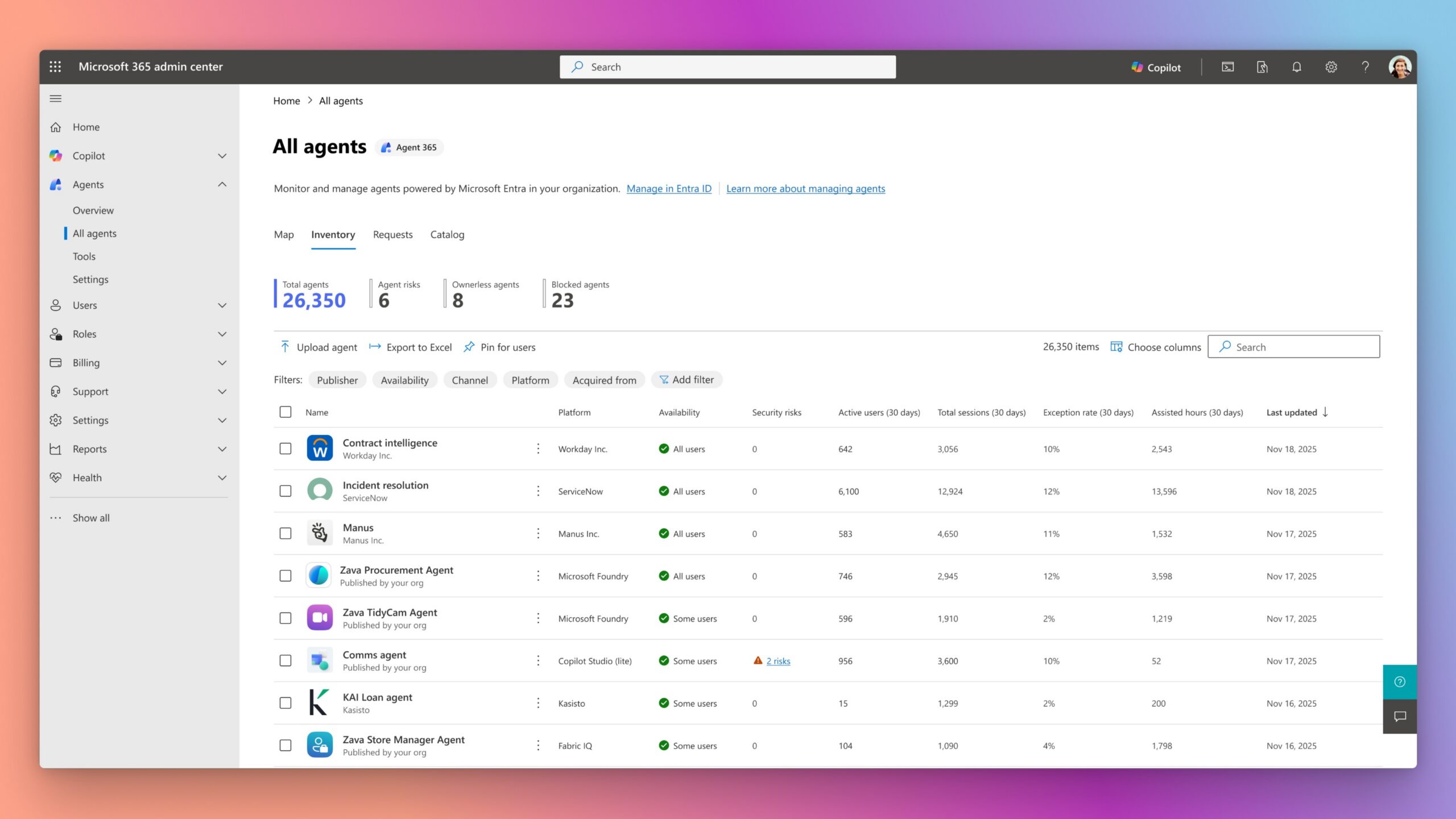
- Registry - centralized inventory of every agent, including shadow agents
- Access control - using Microsoft Entra Agent ID for least-privilege identity
- Visualization - dashboards for performance, connections, and business impact
- Interoperability - works with agents from Microsoft, open-source frameworks, and third-party platforms
- Security - integrated with Microsoft Defender, Microsoft Entra, and Microsoft Purview
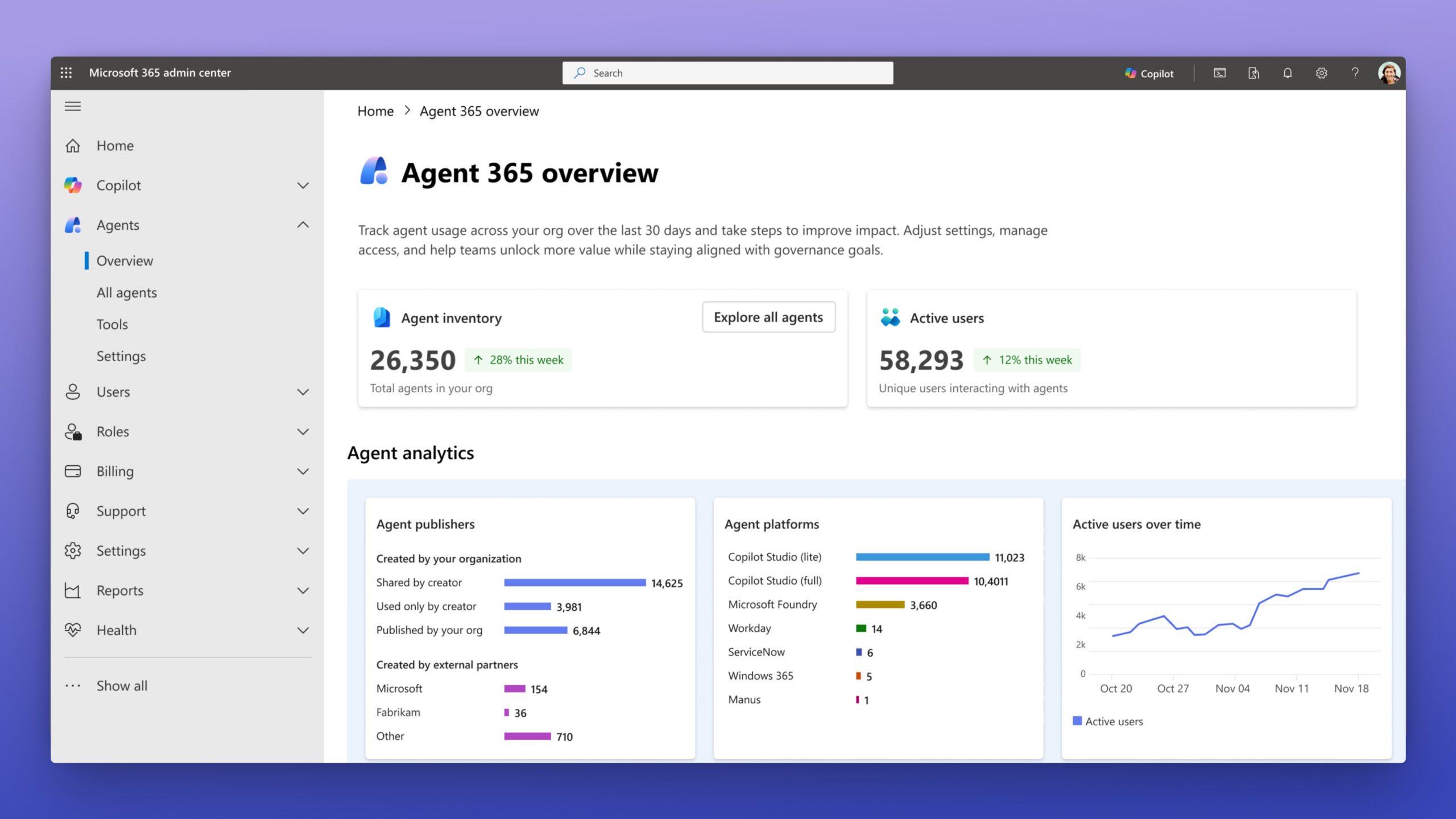 Agent 365 surfaces agent inventory and key analytics inside the Microsoft 365 admin center.
Agent 365 surfaces agent inventory and key analytics inside the Microsoft 365 admin center.
The reality check: agents are scaling faster than governance
Organizations are already seeing the classic pattern:
- Business teams ship Copilot Studio agents quickly
- Pro-code teams build custom agents with Agent Framework
- Vendors introduce third-party agents into Teams and Microsoft 365
- Nobody has a single, trustworthy view of all agents running in the tenant
Agent 365 is Microsoft’s answer to agent sprawl. But the product cannot fix the absence of ownership, policies, or identity hygiene - only your program can.
Build the house from the ground
Treat Agent 365 like the walls and roof of your AI program. Walls only work on a solid foundation. If you skip the foundation, you end up with governance that looks nice in a slide but cracks under real usage.
Foundation layers to put in place before GA:
-
Ownership Define who owns AI agent lifecycle, who owns security, and who owns compliance. Typically this is a joint model between IT, security, data, and platform CoE.
-
Identity Microsoft Entra Agent ID is the access-control anchor. Agents should have identities, not shared credentials, and should follow least-privilege principles.
-
Classification Classify agents by risk - internal productivity, customer-facing, data-modifying, regulated-data. Governance intensity should match risk tier.
-
Data boundaries Use Microsoft Purview for sensitivity, data loss prevention, and auditability. Agents that consume enterprise data must respect information protection policies.
-
Threat protection Use Microsoft Defender for runtime protection and incident response. Agents add new attack surfaces like prompt injection, tool abuse, and data exfiltration via tools.
-
Observability Decide what you will monitor - agent usage, success rate, tool invocations, failures, cost, and drift. Agent 365 provides dashboards, but you must know what “healthy” looks like per agent type.
A simple 30/60/90 plan to be ready
First 30 days
- Produce an agent inventory across Copilot Studio, custom agents, and third-party agents.
- Identify shadow agents that were not registered through IT.
- Assign owners per agent (business owner + technical owner).
Days 30 to 60
- Enable Microsoft Entra Agent ID readiness for production agents.
- Expand Microsoft Purview scope to cover agent data flows.
- Stand up a risk tiering model and map each agent into a tier.
Days 60 to 90
- Enable Agent 365 on the environments that matter most.
- Establish weekly governance reviews of usage, risk, and incidents.
- Publish the AI agent operating model internally - makers need to know the rules.
Why this matters for enterprise leaders
AI agents are starting to act like a digital workforce. That means you need:
- An HR-style lifecycle for agents (onboarding, access, deprecation)
- A security model for non-human identities
- A financial model for cost attribution
- A compliance model for auditability
Agent 365 gives you the product surface to do this consistently. But the operating model has to be owned by you, not by the tool.
Common mistakes to avoid in the GA window
- Treating Agent 365 as a license purchase only - it is an operating model change, not just a SKU
- Starting with tooling before ownership - without accountable owners, dashboards are ignored
- Ignoring shadow agents - unregistered agents represent the biggest real risk
- Skipping risk tiering - if every agent has the same controls, high-risk ones are under-governed and low-risk ones are over-governed
- Relying on one-time reviews - agent behavior, prompts, and tools change constantly; governance must be continuous
What to do this week
- Nominate an Agent 365 program owner
- Start the agent inventory
- Align IT, security, and data teams on a shared AI governance baseline
- Put a May 1 readiness checkpoint on the calendar
The organizations that will benefit most from Agent 365 on day one are not the ones with the most agents. They are the ones with the clearest foundation. Build the house from the ground - identity, classification, data, threat, observability, ownership - so Agent 365 becomes the control plane you already needed, not a dashboard nobody trusts.


💬 Comments & Suggestions
Share your thoughts, tips, or drop a useful link below.